Hi-Performance Ethernet/IP Server with Field Expandable Connections for DataCenter, Replication, and Headquarters sites
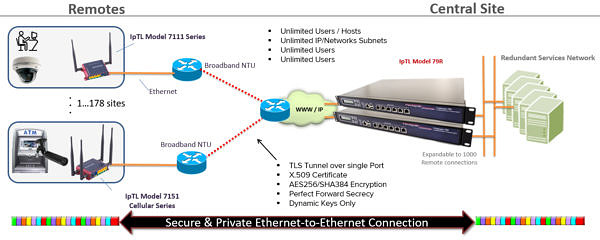
The IpTL Model 79R Series provides a unified management point for terminating large networks. For larger enterprise applications with many sites or as part of an integrated disaster recovery installation, the Model 79R provides the transparency, the bandwidth, and the flexibility for each of your local or remote network connections.
When to Use
- Central site aggregation for up to 1000 remote connections
- Hi Performance Datacenter-to-Datacenter Links
- Network Segmentation of Remotes
- MPLS leased-line link and trunk protection
Ideal Applications
- Hi Capacity 1-1000 connections for IoT & M2M Connectivity, Security, & Cloud Trunking
- Performance WAN Failover & Restore Access Link Protection
- Aggregation of IP Camera Remote Access VPN and Security
- Datacenter site-2-site links and protection
- Large compute data replication cloud connectivity
- MPLS leased-line Failover protection
What you should know
- Connect up to 1,000 remote IpTL appliances and Connect and Extend any Ethernet device over any Dynamic IP Internet with full security
- Start with 25 links and field-expand up to 1,000 remote links with connection licenses without ripping out hardware or downtime
- Concentrates your multisite remote IoT or M2M devices to your headend applications seamlessly with security and control end-to-end so that your data flows between your devices and applications
- MPLS or Lease-line redundancy over Internet with Active/Active redundancy keeping your links up and running and your data flowing without worrying about which path is active
- Load-Balance and Link Aggregation supporting up to 64 independent network connections providing true reliable connectivity so you can get the reliability and throughput your applications demand
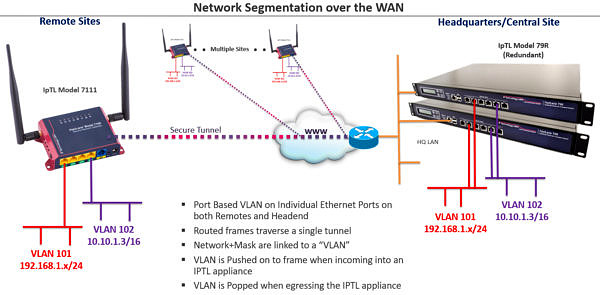
Redundant Network Segmentation and Aggregation
Connect and extend your network resources to multiple sites while keeping your physical networks separated. With multiple Ethernet ports, the Model 79R can split-out individual physical networks – with or without VLANs – and present them over any IP network to remote sites.
Stacking up Model 79R provides redundancy for always on reliable connectivity to all the remotes.
Access Control Integration with LTE Cellular Failover
Connect your remote Access Control readers and IoT/M2M terminals to your controller without the headaches of a traditional VPN router. With IpTL you can connect without any networking blocks or having to configure remote routers at your customer site.
Operating at L2/Ethernet IpTL “hides” the underlying network – including those that block you like NATs, Dynamic IP, Firewalls, Filters, & Proxys – to give your system a secure and transparent end-to-end link.