All Access Pass with built-in LTE, Wi-Fi, Ethernet, Secure Remote Access, & Integrated Battery
IpTL FastLane™ appliances are designed for always-up reliable secure access connectivity. Great for IoT/M2M, Automatic WAN Cellular Internet Failover, Out-of-Band Management, & remote branch applications. We tightly integrate a cellular LTE broadband Internet modem, a full-featured access VPN router, & our patent-pending SystemMontior™ fastest WAN Cellular Internet Failover & Restore switching features.
The 840 includes all the expected networking features. We ensure your project success by including dynamic circuit protection, routing/forwarding, VLANs, and stateful inspection firewall. In addition to the LTE modem, the 840 Series provides wireless 802.11 b/g/n 1×1 AP & simultaneous Wi-Fi Client as well as Ethernet interfaces for reliable always-on secure access to all your network resources. The optional integrated 5000 mAh Li-Po Battery provides network access anywhere anytime.
When to use
- Remote Internet Access over the Cellular Network
- Internet failover redundancy for your existing access network
- Secure IoT/M2M connectivity from device-to-cloud
Ideal Applications
- Mobile Users and Workgroups
- Digital Signage Connectivity
- Kiosks, ATMs, Point of Sale systems, & Lottery machines
- Point IoT & M2M Connectivity & Cloud Trunking
- Cellular Internet Failover & Restore for WAN Protection
- Out of Band Management Access remote equipment access
- IP Camera Remote Access VPN and Security
- Access Control, IO, Intelligent Readers & Network-based Controllers
- Building Automation Systems HVAC Maintenance, monitoring & control
What you should know
- Secure Connectivity any where with integrated LTE Modem, Wi-Fi AP & Client, Wired Ethernet, and 5000mAh battery
- Any interface can be used as tunnel/VPN uplink or user data access
- Integrated Captive Portal option ensure only authorized users can access
- Integrated Access Router and NAT/ACL/Staefull Firewall standard
- Can use Cellular LTE or Wi-Fi or Ethernet as failover/restore interfaces with SystemMonitor automatic switching
- Includes tunnel bonding and data whitening features to secure in-transit links
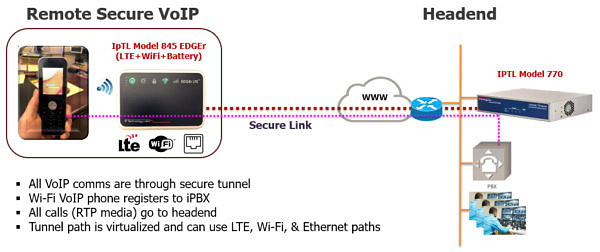
Secure VoIP Mobility
Truly secure voice communications is tough. Exposing VoIP and SIP communications to the Internet is an invitation to eavesdropping or fraud through hi-jacked communications. And Session Boarder Controllers can’t help either.
The IpTL Model 840 EDGEr appliance enables you to keep your all your comms private without without modifying your VoIP equipment. The end-to-end path is transparent to the VoIP endpoints and functions with the iPBX just like it is connected locally.
Wrapped in the latest security, IpTL keeps your good data protected in transit, hides access to your activity and applications, while keeping the bad guys out.
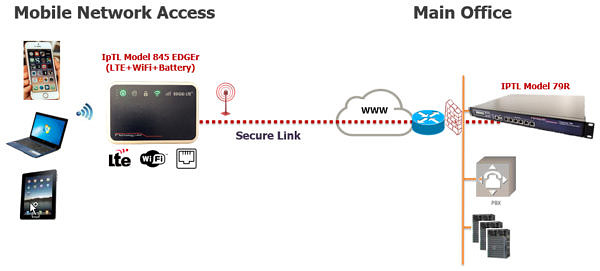
Mobile Secure Networking
Connect to your office anywhere anytime. The Model 840 EDGEr can use any local Wi-Fi hotspot as an uplink and simultaneously provide you a private local Access Point that will connect you to all your office resources. But if you are out-and-about with no Internet, the integrated LTE will automatically switch on and keep you connect without a hitch.
With IpTL you can connect without any networking blocks or the need to configure remote routers at your customer site. Operating at L2/Ethernet, the IpTL VPN “hides” the underlying network – including those that block you like NATs, Dynamic IP, Firewalls, Filters, & Proxys – to give your system a secure and transparent end-to-end link.
The multi-level captive portal login and device MAC ACL’s ensure that no one but you and your authorized users can access your network.